FDA's 3rd Cybersecurity Guidance in 3 Years: What Actually Changed?
FDA released its 3rd cybersecurity guidance in 3 years. Sounds scary. It's not. The update swaps QSR for QMSR and leaves the 14 required cybersecurity documents untouched. Here's what you actually need to know.
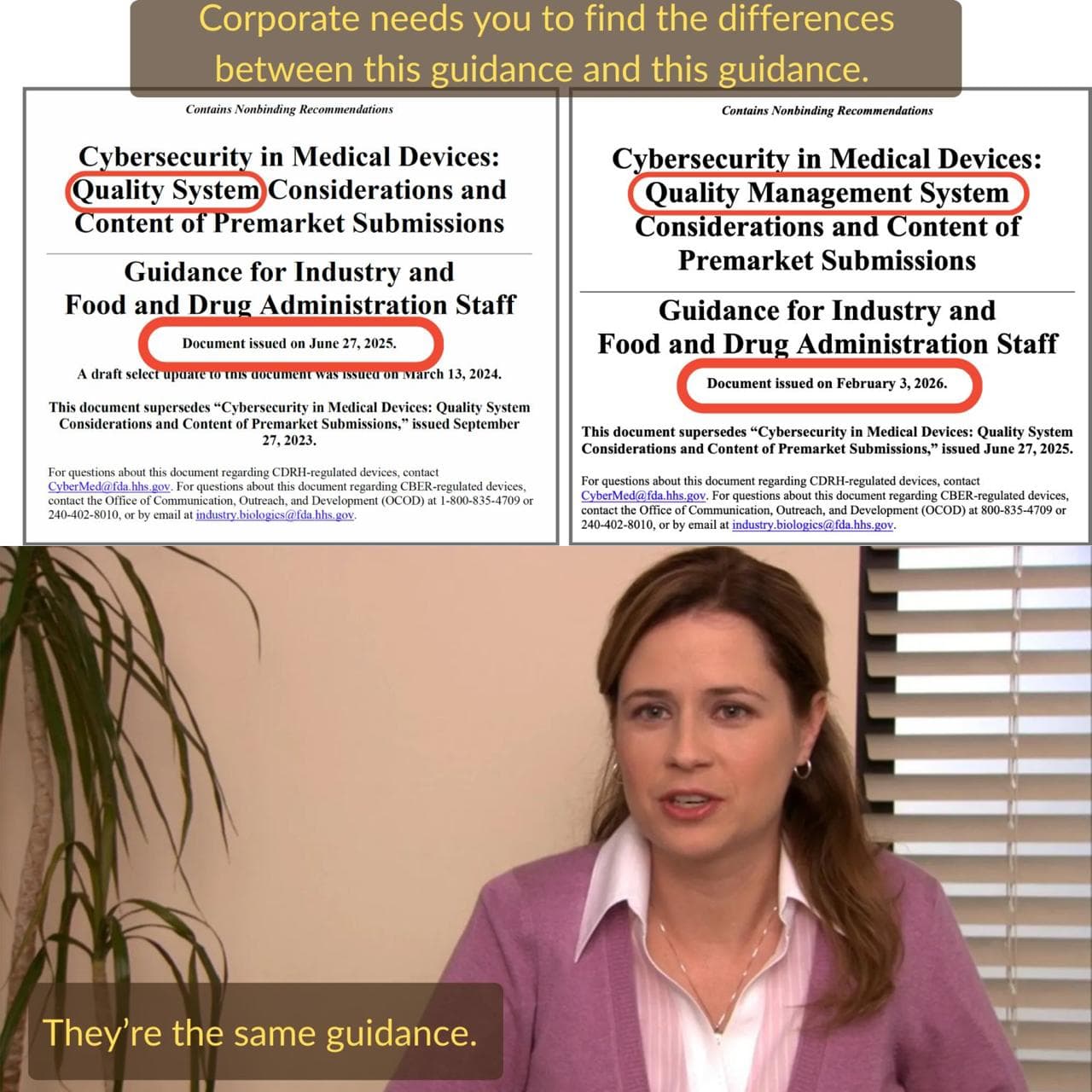
On Tuesday, February 4th, FDA dropped a new cybersecurity guidance. The third one in three years.
When I saw the announcement, my first thought was "great, there goes my weekend." Three guidances since 2023? That sounds like a moving target. It sounds like FDA keeps changing the rules.
But then I read it. And honestly? Not much changed.
FDA basically did a Ctrl+F: "QSR," Replace with: "QMSR." OK, maybe not quite that limited. But close.
Three Guidances, One Timeline
Here's how we got here (our guide chapter on the evolution of FDA cybersecurity requirements traces the longer arc):
September 2023 was the original final guidance under Section 524B. This was the big one. New law, new requirements, 14 cybersecurity documents you need in your premarket submission. Everyone scrambled.
June 2025 brought the first update. About 1,300 tracked changes, which sounds terrifying until you realize most of them were clarifications. The actual requirements didn't move.
February 4, 2026 is what we're talking about now. FDA released this two days after the QMSR took effect on February 2nd. The timing tells you everything you need to know about what changed.
What Actually Changed
The Quality System Regulation (QSR) under 21 CFR Part 820 is gone. Replaced by the Quality Management System Regulation (QMSR), which incorporates ISO 13485:2016 by reference.
The cybersecurity guidance had to reflect that. So FDA updated the references. QSR became QMSR. Quality system language now points to ISO 13485. The guidance also added ISO 9000:2015 Clause 3 for definitions.
That's... pretty much it for the cybersecurity-specific content.
If you were already aligned with ISO 13485 (and most companies selling internationally were), you're in good shape. If your quality system was built entirely around old Part 820 language, you have a bigger project on your hands. But that project is a QMSR transition project, not a cybersecurity project.
What Didn't Change: Your 14 Documents
This is the part that matters. The 14 cybersecurity documents FDA expects in your premarket submission are the same ones from the 2023 and 2025 guidances. All 14 carry forward. Our guide chapter on understanding eSTAR requirements covers how they fit into the submission.
1. Security Risk Management Report. Your complete risk management output, following ISO 14971, specific to cybersecurity. Not a copy of your safety risk file with "cyber" pasted in. A real analysis of security threats to your device.
2. Threat Model. Who would attack your device, why, and how? This needs to be specific to your architecture, your data flows, your deployment environment. Generic threat models get kicked back.
3. Cybersecurity Risk Assessment. Distinct from the threat model. This is where you evaluate likelihood and impact, apply CVSS or a similar scoring framework, and show your residual risk is acceptable.
4. Software Bill of Materials (SBOM). Every software component, version, supplier, and license. Machine-readable format preferred. This is the one that trips up companies the most because it requires knowing exactly what's in your software stack. All of it.
5. Software Level of Support. How long will you support this device? What happens when a third-party component reaches end-of-life? FDA wants a plan, not a vague commitment.
6. Safety and Security Assessment of Cybersecurity Vulnerabilities. You've scanned for known vulnerabilities. Now show FDA how each one affects (or doesn't affect) your device's safety and security profile.
7. Assessment of Unresolved Anomalies for Cybersecurity Impact. Bugs happen. Some ship with the product. FDA wants to see that you've evaluated every known anomaly for cybersecurity implications and made a deliberate decision about each one.
8. Cybersecurity Metrics. How are you measuring the effectiveness of your cybersecurity program? Patch response times, vulnerability discovery rates, time-to-remediation. Pick metrics that actually tell you something.
9. Cybersecurity Controls. The technical controls you've built into the device. Authentication, encryption, access control, audit logging, whatever applies to your specific architecture.
10. Security Architecture Views. Diagrams showing data flows, trust boundaries, external interfaces, and where your security controls sit. FDA reviewers need to see the whole picture, not just a list of features.
11. Cybersecurity Testing. Penetration testing, fuzz testing, static analysis (SAST), dynamic analysis (DAST). Show your work. Include the results, not just a statement that testing was performed.
12. Cybersecurity Management Plan. Your post-market plan. How will you monitor for new vulnerabilities? How will you handle coordinated vulnerability disclosure? What's your patch cadence?
13. Cybersecurity Labeling. What do users need to know about your device's cybersecurity? Network requirements, supported configurations, hardening instructions, end-of-support dates.
14. Interoperability Risk Assessment. If your device connects to other systems (and it probably does), how do those connections create risk? Hospital networks, cloud services, mobile apps, other devices in the ecosystem.
That's the list. Same list as 2023. Same list as 2025. Same list today.
The QMSR Transition Matters (Just Not Here)
I don't want to undersell the QMSR change. It's a big deal for your quality system. ISO 13485 becoming the law of the land in the US changes how you structure your design history files, how purchasing controls work, how you handle document control. Plenty of LinkedIn ink has been (rightfully) spent on this topic.
But for your cybersecurity submission? The practical impact is limited. Your 14 documents still need to exist. They still need the same content. The difference is that they now sit within an ISO 13485 quality management framework instead of the old Part 820 framework. If your QMS was already dual-tracked for international markets, this is almost a non-event.
What You Should Do
Check your references. Open your cybersecurity SOPs, templates, and procedures. If they say "QSR" or "21 CFR Part 820," update them to reference the QMSR and ISO 13485:2016. This is a find-and-replace exercise. (Sound familiar?)
Map your cybersecurity docs to ISO 13485. Your threat model is a design output under Section 7.3. Your SBOM fits within purchasing controls under Section 7.4. Your cybersecurity management plan is part of post-market surveillance. Make sure these connections are explicit in your QMS.
Don't start over. If you built your cybersecurity program around the 2023 or 2025 guidance, you're fine. Update the QMS references, make sure everything still traces correctly, and keep going.
Do check your SBOM and threat model. Not because of this guidance update, but because those are the two documents we see rejected most often. Are they current? Complete? Machine-readable?
And if you haven't started your cybersecurity documentation yet, the 14-document list hasn't changed. That's good news. It means every resource, template, and guide that existed before February 4th still applies.
Get the Full Breakdown
We wrote a complete guide to all 14 cybersecurity documents FDA expects in your submission. It walks through each one with examples, common mistakes, and what FDA reviewers actually look for.
And if you want help getting all 14 done right (and done fast), CyberSprint delivers a complete cybersecurity documentation package in 30 days. Mapped to QMSR. Ready for submission.
Talk to us if you're working on a submission and need a second set of eyes. Or a first set.