How to Systematically Identify Cybersecurity Threats and Meet FDA Requirements
Summary
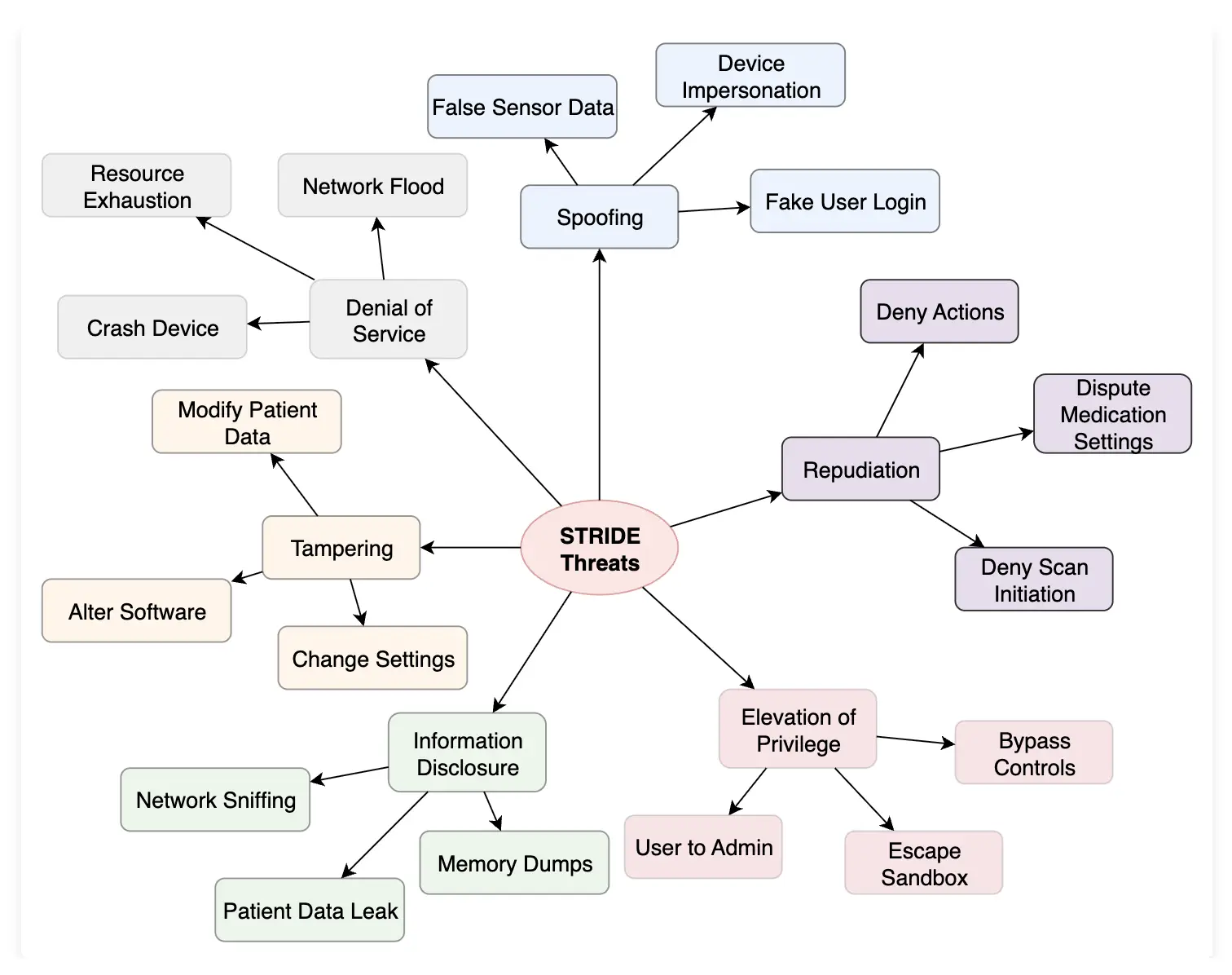
STRIDE for medical devices provides a systematic approach to identifying cybersecurity threats throughout the device development lifecycle. This comprehensive framework helps quality, regulatory, and engineering teams categorize threats into six distinct categories: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. By implementing STRIDE for medical devices, teams can build more secure products that meet FDA cybersecurity requirements while protecting patient safety.
What you’ll learn from this article:
- How to apply the STRIDE threat modeling framework to medical device development
- Six categories of cybersecurity threats specific to healthcare environments
- Real-world examples of each STRIDE threat type in medical devices
- Practical defensive strategies aligned with FDA cybersecurity guidance
- Step-by-step implementation guidance for regulatory submissions
Medical device cybersecurity has become a critical regulatory requirement. The FDA’s 2025 cybersecurity guidance mandates that manufacturers demonstrate systematic threat identification and risk management. STRIDE for medical devices offers a proven methodology that satisfies these requirements while providing practical security benefits.
STRIDE stands for Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. This framework, originally developed by Microsoft, has been adapted for healthcare environments where patient safety and data protection are paramount concerns.
Understanding the STRIDE Framework for Healthcare
STRIDE for medical devices differs from traditional IT threat modeling because it addresses unique healthcare challenges. Medical devices operate in environments where security failures can directly impact patient safety. Unlike consumer software, medical devices often have extended lifecycles, limited update capabilities, and must maintain availability in critical situations.
The framework aligns with several key regulatory documents:
- FDA’s 2025 Guidance on Device Cybersecurity for Premarket Submissions
- ANSI/AAMI SW96:2023 (which incorporates and builds upon TIR57)
- ISO 14971:2019 for risk management
- IEC 62304 for medical device software lifecycle
The Six STRIDE Threat Categories Explained
Spoofing: Identity and Authentication Attacks
Spoofing threats target authentication mechanisms and identity verification systems. In medical devices, these attacks can have severe consequences because they undermine trust in device communications and user authentication.
Common spoofing threats in medical devices include:
- False sensor data injection
- Device impersonation on networks
- Fake user login credentials
- Malicious applications pretending to be authorized software
For example, an attacker might spoof glucose meter readings to an insulin pump, potentially causing dangerous dosing decisions. This type of attack exploits weak authentication between connected devices.
Defensive strategies against spoofing:
- Implement strong cryptographic authentication
- Use digital certificates for device-to-device communication
- Deploy multi-factor authentication for user access
- Validate sensor data through secondary verification methods
Tampering: Unauthorized Modification Attacks
Tampering involves unauthorized changes to device software, configuration, or data. These threats are particularly concerning in medical devices because they can alter clinical functionality without obvious signs of compromise.
Medical device tampering examples:
- Modifying patient data in electronic health records
- Altering software configurations
- Changing device settings or parameters
- Installing unauthorized applications
Consider an infusion pump where an attacker modifies dosage calculations in the software. Such tampering could lead to over-dosing or under-dosing without triggering obvious alarms.
Protection against tampering:
- Implement integrity checking mechanisms
- Use code signing for software updates
- Deploy configuration management controls
- Monitor for unauthorized changes
Repudiation: Accountability and Non-Repudiation Issues
Repudiation threats involve disputes about actions taken within the medical device system. These are particularly important in healthcare due to legal and financial liability concerns.
Healthcare-specific repudiation threats:
- Clinicians disputing medication administration settings
- Denying responsibility for scan initiation that led to patient harm
- Disputing device configuration changes
- Questioning the authenticity of clinical actions
The MITRE Playbook for Threat Modeling Medical Devices emphasizes that repudiation threats should focus on areas with “monetary or legal impact to subverting the process.” In healthcare, these situations frequently arise during patient safety investigations.
Addressing repudiation threats:
- Implement comprehensive audit logging
- Use digital signatures for critical actions
- Deploy non-repudiation controls
- Maintain detailed timestamps and user tracking
Information Disclosure: Data Privacy and Confidentiality Breaches
Information disclosure threats expose sensitive patient data or device information to unauthorized parties. These threats violate HIPAA requirements and can compromise patient privacy.
Common information disclosure scenarios:
- Network sniffing of unencrypted communications
- Patient data leaks through insecure interfaces
- Memory dumps revealing sensitive information
- Unauthorized access to diagnostic data
For instance, unencrypted Bluetooth communications from a cardiac monitor could expose patient vital signs to nearby attackers with radio frequency monitoring equipment.
Preventing information disclosure:
- Encrypt all data in transit and at rest
- Implement access controls and data classification
- Use secure communication protocols
- Regular security assessments and penetration testing
Denial of Service: Availability and Operational Disruption
Denial of Service (DoS) attacks prevent legitimate users from accessing device functionality. In medical environments, availability disruptions can have life-threatening consequences.
Medical device DoS attack vectors:
- Network flooding to overwhelm communication channels
- Resource exhaustion attacks
- Intentional device crashes
- Battery depletion attacks on portable devices
A real-world example might involve flooding a wireless patient monitoring system with bogus connection requests, preventing nurses from receiving critical patient alerts.
DoS protection strategies:
- Implement rate limiting and traffic filtering
- Design fault-tolerant architectures
- Use watchdog timers and automatic recovery
- Isolate critical functions from network dependencies
Elevation of Privilege: Unauthorized Access Escalation
Elevation of Privilege (EoP) attacks allow attackers to gain higher-level access than intended. These threats can compromise entire medical device systems and connected networks.
Privilege escalation examples in healthcare:
- Users gaining administrative access to device management systems
- Escaping application sandboxes
- Bypassing access controls
- Exploiting vulnerabilities to gain system-level access
An example would be a patient portal vulnerability that allows one patient to view all patient records rather than just their own data.
Preventing privilege escalation:
- Implement principle of least privilege
- Use role-based access controls
- Regular security code reviews
- Deploy application sandboxing and isolation
Implementing STRIDE for Medical Devices
STRIDE for medical devices requires a systematic approach that integrates with existing development processes. The implementation should align with your medical device secure software development lifecycle and risk management procedures.
Step 1: Create Data Flow Diagrams
Start by developing comprehensive data flow diagrams that show how information moves through your device system. These diagrams provide the foundation for systematic threat identification.
Step 2: Apply STRIDE Per Element
Use the STRIDE per Element approach recommended by the MITRE Playbook. This method maps specific STRIDE threats to different diagram elements:
- External entities: Spoofing and Repudiation
- Processes: All six STRIDE categories
- Data stores: Tampering, Information Disclosure, and Denial of Service
- Data flows: Tampering, Information Disclosure, and Denial of Service
Step 3: Document Identified Threats
Create a comprehensive threat register that captures each identified threat with sufficient detail for risk assessment and mitigation planning. Include threat descriptions, potential impacts, and likelihood estimates.
Step 4: Develop Security Architecture
Use your threat analysis to inform your security architecture design. Ensure that your cybersecurity controls address the specific threats identified through STRIDE analysis.
Regulatory Compliance and Documentation
STRIDE for medical devices helps demonstrate compliance with FDA cybersecurity requirements. The systematic threat identification approach aligns with the FDA’s expectation for comprehensive cybersecurity risk management.
Your documentation should include:
- Threat modeling methodology and rationale
- Complete threat inventory with risk assessments
- Mitigation strategies and their effectiveness
- Traceability between threats and implemented controls
Consider creating a cybersecurity traceability matrix that links STRIDE threats to specific control implementations and validation activities.
Integration with Risk Management
STRIDE for medical devices should integrate with your ISO 14971 risk management process. Each identified threat becomes an input to your risk analysis, where you evaluate potential clinical impacts and implement appropriate risk controls.
The relationship between STRIDE threats and patient safety requires careful consideration. Some cybersecurity threats may not directly impact patient safety but could affect data integrity or system availability. Others may have direct safety implications that require immediate mitigation.
Common Implementation Challenges
Teams often face several challenges when implementing STRIDE for medical devices:
Scope Definition: Determining the appropriate boundaries for threat modeling can be difficult, especially for complex, interconnected systems.
Resource Requirements: Comprehensive threat modeling requires significant time investment from cross-functional teams.
Maintaining Currency: Threats evolve over time, requiring regular updates to threat models and associated documentation.
Integration with Existing Processes: Fitting STRIDE analysis into established development workflows requires careful planning and change management.
Tools and Resources
Several tools can support your STRIDE for medical devices implementation:
- Microsoft Threat Modeling Tool (free, STRIDE-focused)
- OWASP Threat Dragon (open source, supports multiple methodologies)
- IriusRisk (commercial platform with medical device templates)
The MITRE Playbook for Threat Modeling Medical Devices provides detailed guidance and examples specifically tailored to healthcare environments.
Beyond Basic Implementation
Advanced STRIDE for medical devices implementation considers the entire product ecosystem, including cloud services, mobile applications, and integration with hospital networks. This holistic approach requires threat modeling for cloud-connected medical devices and consideration of supply chain security.
Modern medical devices often require sophisticated software update mechanisms and patch management processes. These capabilities must be designed with security in mind from the beginning.
Conclusion
STRIDE for medical devices provides a practical, systematic approach to cybersecurity threat identification that aligns with FDA requirements and industry best practices. By implementing this framework, medical device manufacturers can build more secure products while demonstrating regulatory compliance.
The key to successful implementation lies in treating STRIDE as part of a comprehensive cybersecurity program rather than a standalone activity. Integration with risk management, software development, and quality processes ensures that threat modeling produces actionable results that improve product security.
As medical devices become increasingly connected and sophisticated, systematic threat modeling becomes even more critical. STRIDE for medical devices offers a proven methodology that scales with device complexity while maintaining focus on patient safety and data protection.
Remember that threat modeling is an iterative process. Regular updates to your STRIDE analysis ensure that your security posture evolves with changing threats and device functionality. This ongoing commitment to cybersecurity helps protect patients while supporting regulatory compliance throughout your product’s lifecycle.